Have you ever won a prize that you did not want? Perhaps your name was added to a list that you would rather not have been on. Today there is a list that every company should be aware of. Shodan is a website anyone can use to find open ports on internet connections and, unfortunately, is used with malicious intent.
Blog
The State of Thunderbolt 3: Part 2
Looking for “The State of Thunderbolt 3, Part 1?” Click here.
Recently, I was in my home office working on my computer. I have a 27-inch 4K monitor, USB Apple Keyboard, Wireless Mouse, speakers, Logitech webcam, laser printer, and an ethernet connection to my network.
Looking for “The State of Thunderbolt 3, Part 1?” Click here.
Recently, I was in my home office working on my computer. I have a 27-inch 4K monitor, USB Apple Keyboard, Wireless Mouse, speakers, Logitech webcam, laser printer, and an ethernet connection to my network.
Google has been waging war against the non-secured website for years. In 2016, Google made a pledge to start shaming websites with un-encrypted connections, as way to encourage developers to embrace HTTPS. With Google Chrome 68, the latest version of the popular web browser, Google is following through on its promise.
Design in the workplace is no longer confined to the Marketing or Sales department. When paired with critical business statistics or financial numbers, visual charts and graphics can dramatically increase business efficiency. Software developers know a picture is worth a thousand words.
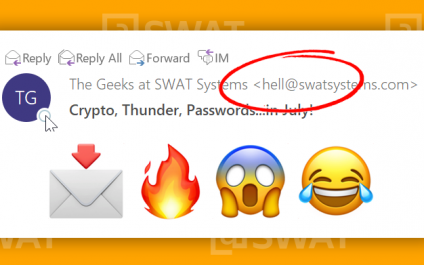
Several of our monthly newsletter readers noticed that our July 2018 edition was delivered to them from a unique SWAT email address. The email address that raised eyebrows? hell@swatsystems.com.
“We’re you hacked? Is this a phishing scam? Did a disgruntled employee sabotage your newsletter?”
No, no, and no.
“We’re you hacked? Is this a phishing scam? Did a disgruntled employee sabotage your newsletter?”
No, no, and no.
“All good things must come to an end” will ring loud and clear come January 2020. Like with all of Microsoft’s operating systems, Mainstream and Extended Support is provided by Microsoft for a period of time. Microsoft calls its products “End of Life” when the Extended Support period comes to an end.
Recently, I was in my home office working on my computer. I have a 27-inch 4K monitor, USB Apple Keyboard, Wireless Mouse, speakers, Logitech webcam, laser printer, and an ethernet connection to my network. You should know, however, that my computer is a 2017 Macbook Pro laptop and the only thing connected to my laptop is a single Thunderbolt 3 cable.
The Password Dilema
Now matter your age, job, or hobby, if you are someone who uses any piece of technology or online service, you have a password. Our digital accounts are protected by these things, which means we have a lot of them! I’m working on creating a support group that helps people overcome pain and suffering from tracking multiple password.
Now matter your age, job, or hobby, if you are someone who uses any piece of technology or online service, you have a password. Our digital accounts are protected by these things, which means we have a lot of them! I’m working on creating a support group that helps people overcome pain and suffering from tracking multiple password.
There is an old saying, “safety in numbers.” As we tend to see in nature, wildebeest, zebra, fish, birds and other animals have relied on this premise for millennia. What we rarely consider though, is that large numbers can also attract the unwanted.
On July 14, 2018, we flipped a game night on its head and hosted a game day at the office. The sun was out, giving us the perfect weather for grilled chicken and hot dogs. With I-5 mostly closed, several of our peeps were unable to make it. Regardless, we had a great group of people and games that make any situation a whole lot of fun! Below are a few that are considered a favorite at SWAT Systems.